Virtualization quickly went from buzzword to standard tool for developer and ops staff alike. But its cousin, the virtualized network, has taken a little longer to come of age and become popular. But now that cloud hosting has become commonplace, virtualizing the network connections between cloud-hosted servers has become a fashionable way to speed up performance and increase security.
Vyatta, for all intents and purposes, created the network virtualization market single-handedly, starting in 2006. Kelly Herrell, CEO of Vyatta, said that his company focused on layer 2 and 3 networking, rather than sitting higher on the transaction layer totem pole. He said this was the secret to Vyatta’s success.
“Nobody tried to come at this layer 3 networking problem before,” he said. “The only way you did this was with proprietary Cisco routers. We had a lot to prove, and our community helped us prove that thanks to our free download. Layer 3 is a very important thing, so layer 2 and 3 are the network. Layers 4 through 7 make the network better, and they’re where you’ll do load balancing, WAN optimization and firewalling, but layer 2 and 3 are your fundamental networking layers.
“Cisco had 90% market-share when we started, and they got that through proprietary protocols. The Internet has removed that need, so you can start to use a vendor of heterogeneous networks. That was the beginnings of a long decline toward standardization.”
Vyatta’s product, at the start, was a Linux distribution that, essentially, is a router. The company’s software includes all the complex capabilities an expensive router contains: load balancing, firewalling, WAN optimization, NAT, DHCP server, and a host of other network-focused services that allow developers and ops people to configure and deploy Vyatta-based routers into any cloud environment. The company has since expanded and refined its product line.
“One of the things we see as the core factor for adoption is literally the application storm that’s going on,” said Herrell. “Looking back on it, it’s probably driven by the fact that people have fairly unfettered access to software development tools. Not too long ago it was negotiations, receipts and purchases, but now you just download things online. There’s a storm of application deployment going on. From an IT side, they’re responsible for getting the gear to run, and creating large generic pools of virtualized compute to put the applications on.”
Herrell said that in many sales meetings, the room will be packed with software developers and IT administrators. After a demonstration of the product, he said the IT folk will often look at the software development people and say, “If we use this, then you can do all those things I won’t let you do.”
The point being, said Herrell, that when cloud-based machines are on their own private network with the database servers, developers are free to pass encrypted packets back and forth freely. When those servers are just out in the open on the cloud host’s network, security and communication integrity can be a major concern.
Raj Kanaya, cofounder and CEO of WAN-optimization company Infineta Systems, said that network virtualization will only become more commonplace as standards emerge. “You have new technologies and standards like VMware’s VXLAN,” he said. “That’s taking traffic IP packets and encapsulating them in such a way that you can have overlapping address spaces and so forth. The net of it is with network virtualization; the challenge for the WAN optimization players is that it gets more complex to actually crack open the packets and inspect them.”
He also added that his company’s hardware-based approach can handle that increase in complexity. It all comes down to being clever.
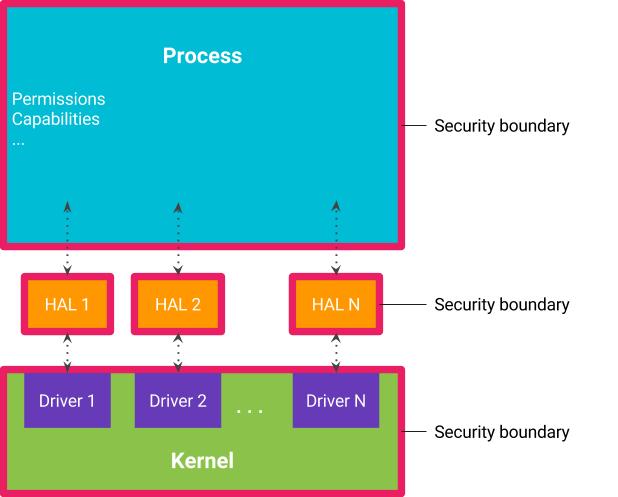
And Vyatta has included some serious cleverness in its most recent versions of its platform. “All network devices have a control and forwarding plan,” said Herrell. “For Vyatta, the control plan and forwarding plan have always been welded into the same software. One of the things we’ve done recently, we’ve architecturally separated the control plan from the forwarding plan. One of the reasons we did this is because as servers get more and more densely packed with VMs, and as these servers are getting more powerful, we can do more. Think of someone taking a rack out of commission after three years. Those were two-core virtual servers. Now you’re replacing them with 20 cores. You’re going to have a lot of applications in there.
“That means you’ve got 70x the amount of network traffic in and out of that server. One of the things we saw coming was the need for Vyatta to scale to previously unprecedented heights. When we separated these planes, the forwarding vPlane [Vyatta’s software that allows end nodes in the network to participate in the virtualized network] sitting on a core can do 8 million packets per second. You put a vPlane on each core and it multiplies because it scales linearly. We bypassed a whole bunch of schedulers in Linux and some others in the virtual network interface card. By bypassing these schedulers, we can do a run to completion model under the hood and handle packet forwarding at clock speed.”