Companies face a terrible choice. Either transform their business into software and accept rampant vulnerabilities and breaches, or lose the innovation race with their competitors. Companies always choose software – there will be 111 billion lines of new code written in 2017, according to a Cybersecurity Ventures report. And our traditional approaches simply aren’t anywhere close to being able to prevent vulnerabilities and attacks at that scale.
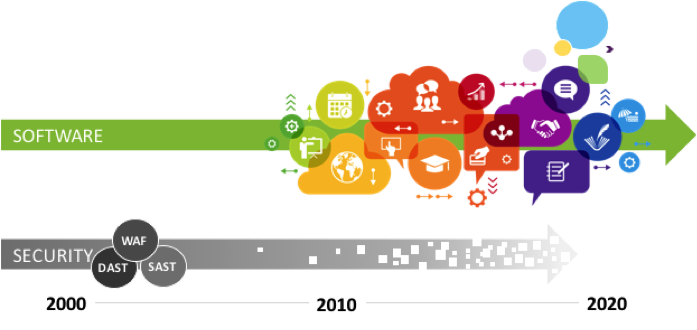
Traditional tools can’t keep up with modern software
That sounds bad. But actually, it’s worse. Applications are changing. Fast. The “website” you used to know was a single application running on a server in a datacenter somewhere. Today, that same website might look the same to the user, but under the hood it’s completely transformed. The user interface is now written in JavaScript that runs the browser. The server-side has morphed into a set of REST APIs. And the code runs in containers like Docker, expands elastically based on demand, and is deployed multiple times a day!
Legacy security tools from the early 2000s, like static code scanners, dynamic scanners, and web application firewalls were never great protection for applications. But containers have removed the physical constraints of servers and hardware, allowing software development to automate and accelerate. These old security tools require extensive configuration, tuning, and triage by experts, so they just can’t keep up. This leaves companies with no good alternatives for securing their applications.
Our only hope is to migrate from old monolithic environments with perimeter protection into a new architecture with individually protected applications. Ed Amoroso, former CISO of AT&T, depicts the transformation this way in his treatise for CISOs. First, you “explode” the enterprise into micro segments. Then you “offload” these micro segments to cloud environments. And finally, you “reload” security into these environments.
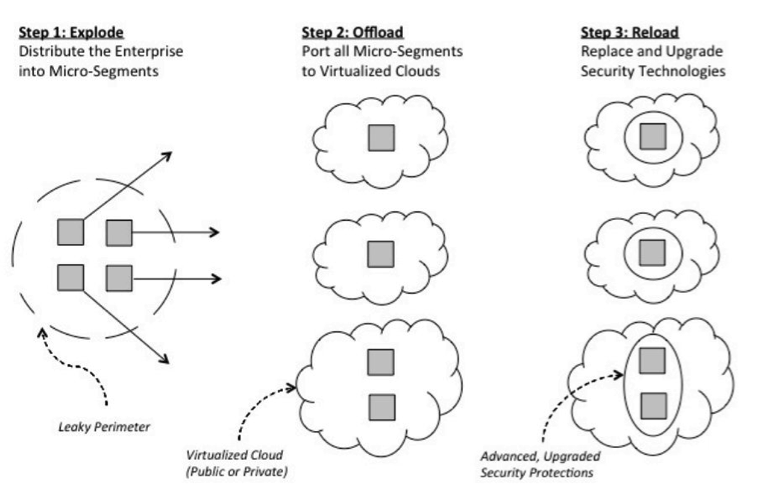
https://www.tag-cyber.com/Annual/2017/Volume%201%20-%20TAG%20Cyber%20Security%20Annual%20-%20Fifty%20Controls.pdf
How do we achieve this transformation at the application layer? When we deploy complex technologies, like planes and nuclear power plants, we instrument them for visibility, safety, and security. But software – the most critical and complex thing man has ever built – has essentially no instrumentation. We’re flying blind.
Software instrumentation has been used for many years for performance and logging. This is the same approach companies like New Relic and AppDynamics use to improve performance in thousands of companies. Security instrumentation has numerous advantages over traditional analysis and protection approaches. Legacy tools fail because they are too far from the applications they protect – they have no “context” to inform their analysis. Imagine the advantages of instrumenting security directly into applications, where it can take advantage of all the information available from the inside.
Accurately detecting vulnerabilities and attacks requires a lot of “context.” For example, some vulnerabilities are only obvious in HTTP traffic. Others can only be detected in source code. And some by analyzing open-source libraries and frameworks. And the vast majority can only be detected accurately by watching how the application actually runs. Instrumentation of applications is the only way this contextual information can be accessed easily and accurately. There is almost no limit to what application information is available through this powerful technique.
Security instrumentation is available now. Technologies called “Interactive Application Security Testing” (IAST) and “Runtime Application Self-Protection” (RASP) are helping organizations transition to a continuous, real time approach to application security. IAST detects vulnerabilities and RASP blocks attacks. Simply by adding IAST and RASP to your applications you can revolutionize application security in your organization. Because IAST and RASP are a distributed approach, as Ed Amoroso described, you’ll have complete and continuous vulnerability and attack telemetry across your entire application portfolio. For the first time, you’ll be able to understand security across your entire application portfolio all at once.
The result is security that works with modern software development, or “DevSecOps” as it’s called. Imagine an entire portfolio of applications, all with defenses like IAST and RASP instrumented in at runtime. Security is distributed and happens in parallel, everywhere. Unlike traditional solutions that are serial, centralized, bottlenecked, and resource constrained, security instrumentation enables security to scale naturally with the applications themselves.
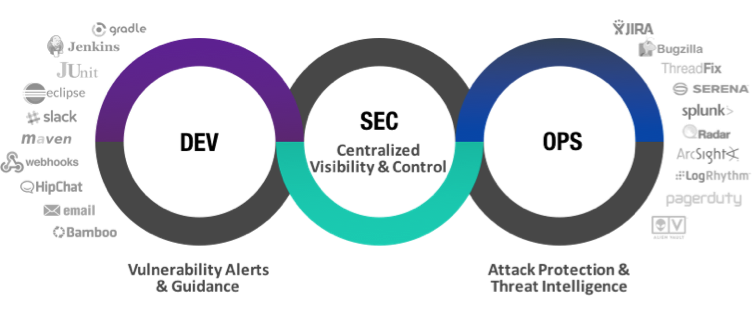
The application of the future can diagnose its own vulnerabilities and protect itself against attacks. Done right, security can accelerate software development as opposed to being a blocker. Developers, testers, and operations should all consume application security notifications in real time, through the tools they are already using. And as network and host security become dominated by cloud and container environments, it shouldn’t matter how or where applications are deployed.
When software is self-protecting, companies can embrace software without sacrificing security.





