Most mobile applications contain at least some programming flaws that make them susceptible to leaking data containing personal information. In fact, mobile applications distributed in Apple’s App Store and Google Play are more likely to have at least one hidden bug that can compromise privacy than they are of containing a security vulnerability, where the likelihood is also alarmingly high, according to a recent assessment.
Mobile software penetration testing provider NowSecure determined in that recent study that 90 percent of applications in the U.S. portions of those marketplaces could potentially leak one or more pieces of personal information.
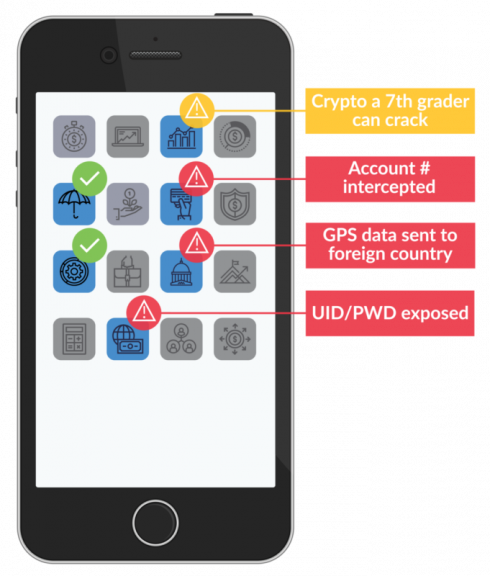
The analysis found that personal data can leak within the confines of the device itself, to another application or in a file over a network, that a hacker can intercept. NowSecure conducted the privacy assessment this spring after it added the ability to scan for potential GDPR violations to its mobile app testing engine. The specter of leaking personally identifiable information (PII) could put an organization at risk of violating GDPR, though it doesn’t mean such a violation will or has occurred.
“It’s kind of stunning,” said Brian Reed, NowSecure’s chief mobility officer. “PII can be a lot of things when you think about mobile. PII isn’t just my username and password, it is also the GPS location.” Reed emphasized that many mobile apps are responsible for sharing a user’s whereabouts, as well as data from a device such as its serial number, International Mobile Equipment Identity (IMEI) or MAC address.
“You’d be amazed at how many of these apps just beacon that stuff out that can be picked up by sniffers, or can be intercepted over the network, either the WiFi or the carrier network,” he said. The finding that 90 percent of mobile apps are at risk of compromising privacy is an exceedingly high figure, but only slightly higher than the percentage that have security vulnerabilities.
Last fall, NowSecure performed a similar analysis of mobile apps and discovered 85 percent had one or more security vulnerabilities, where they specifically violated one or more of the OWASP Mobile Top 10 most critical web application security risks. Reed believes both findings show that securing mobile apps has taken a back seat to web apps. “In the race to build more apps faster, security and privacy are being left behind,” he said.
Consequently, hackers have gravitated to mobile apps as they have become the easier target. “The bad guys have figured out everybody’s hardened their web back end, but they haven’t hardened their mobile apps,” he said.
Perhaps that explains the rise in high-profile breaches affecting mobile apps over the past year. Among them, My Fitness Pal, a subsidiary of Under Armour, last year had to inform 150 million account holders that their information was stolen by hackers. The information surfaced on the dark web, back in February nearly a year after the breach was discovered.
A breach of Air Canada’s mobile app last summer affected 1.4 million customers. Earlier this year, hackers were using the McDonald’s mobile app to steal significant amounts of food from the hamburger chain.
One reason securing mobile apps has fallen to the back burner is that it’s hard to do, Reed said. “Whereas in a browser, you can just make a Java call over HTTPS and it sets up a secure SSL and a TLS connection on your mobile device, with mobile apps you’ve got to actually write that code or download a library to help you do that.”
Given the fact that mobile apps are so susceptible, organizations building customer-facing mobile apps need to address these issues head-on, according to Reed. The first step is to create DevSecOps processes around licensing, building and designing secure components for mobile apps with reusable network connections and encryption.
Next, it’s critical to add continuous testing into the CI/CD process. “Make sure that the code you write every day is getting scanned every day and has that higher bar of security,” Reed said. “And then you should automatically raise the bar of building higher quality software faster, because you’ve got reusable components that are safe.”
Finally, to address the agile nature of today’s continuous approach to mobile application development, automating mobile application security and penetration testing can protect all attack surfaces. NowSecure’s solutions plug directly into their various CI/CD tool chains including CloudBees, CircleCI and Jenkins. Reed said that means “now every build, every day gets an automated security test for any mobile app that they build.”
Content provided by SD Times and NowSecure






