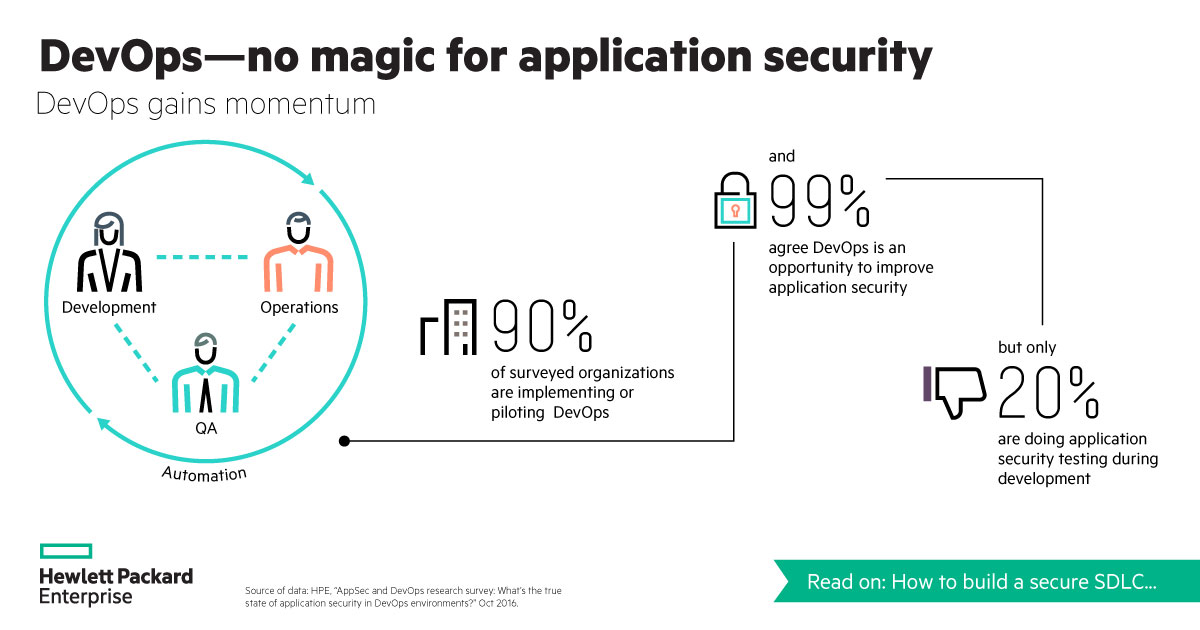
The adoption of DevOps is transforming how companies deliver software, but this shift toward agility and Continuous Delivery is exposing some gaps that persist in application security.
A majority of security teams and developers agree that adopting DevOps into their culture can improve application security, but only a small portion of them actually do application security during development, according to the Application Security and DevOps Report 2016 by the HPE Security Fortify team.
According to the report, 99% of respondents agreed that DevOps culture has the opportunity to improve application security. However, only 20% stated that secure software development life-cycle testing is done throughout their development process. And 17% stated that they are not using any technologies to protect their applications, as most organizations rely on technologies like pre-production penetration testing and network security.
(Related: New industries are taking on software security for the first time)
From this study, the HPE Security Fortify team validated some of the organizational barriers that stand in the way of making application security and DevOps an integral part of the development process.
Before DevOps, development and security teams did not work together, and building security into the development process today means breaking down any silos and sharing the responsibility between application teams, according to Scott Johnson, director of product management for the HPE Security Fortify team.
Factors beside existing silos also lead to the lack of awareness of application security. For instance, the report found that developers do care about security and are trying to learn more about security practices while they work, but their main focus is usually timely deliveries, features and quality software.
“The fact that building security in as part of the development process is just not something that has been historically done [is a barrier],” said Johnson. “Developers aren’t necessarily trained in security; it’s not part of their job descriptions. Universities are just now starting to teach it as part of the curriculum, where in the past, it hasn’t been [taught].”
Also, secure coding practices are often not job requirement. The report looked at more than 100 job postings for software developers at Fortune 100 companies, and none of them specified security, secure coding experience, or knowledge as required skills.
What else ails software security
In addition to these challenges, there are internal factors like a lack of understanding when it comes to security and development leadership, as well as an increasing lack of application security talent. According to the report, there was an average of 900 developers in the organizations surveyed, and in comparison, there were only 11 application security professionals in those organizations, and this ratio makes it a challenge for application security professionals to keep up, according to the report.
These barriers pose key challenges for organizations looking to secure the software development life cycle, which is why the HPE Fortify Team shared a few best practices for secure application deployment and ways to put security into the development process, and not as an afterthought, according to Johnson.
One solution is for organizations to stop working from a top-down and bottom-up approach when it comes to security within their application security for a DevOps environment. Johnson said organizations have to start from the CIO down, but then continue to work from the bottom, where the developers are writing the code. Overall, security should be a shared responsibility to eliminate barriers.
Another solution Johnson suggested organizations consider is to leverage enterprise-grade application security automation with built-in analytics, so security professionals can work on other tasks and not worry about false positives and manual processes.
“There is this whole notion of shifting left in the development life cycle,” said Johnson. “So one of the things that organizations can do is enable their developers to help identify vulnerabilities—application security vulnerabilities—early in the process.”