It’s not enough to keep on top of the most common security issues plaguing software today. Developers should understand exactly what issues are impacting the programming languages they are using. Veracode has released new data that shows the top security flaws affecting .NET, C++, Java, JavaScript, PHP and Python.
“Knowing these trends in application security before you sit down to code means you’re prepared to fix them quickly or – even better – prevent them altogether,” Meghan McBee, senior content marketing manager at Veracode, wrote in a post. “If C++, PHP, .Net, or Java are your languages of choice, take note – they’re prone to some of the riskiest vulnerabilities around. In fact, a whopping 59 percent of C++ applications have high and very high-severity flaws, with PHP coming in at a close second place.”
RELATED CONTENT: Developers buying in to security tasks
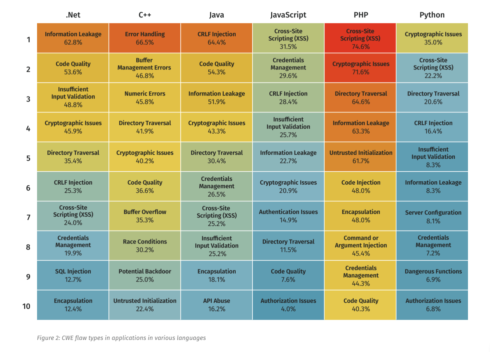
The company put together an interactive heat map to display the top programming languages and their flaws as well as how those flaws can be prevented.
According to the heat map, the top flaws for .NET include: information leakage, code quality, insufficient input, validation and cryptographic issues. C++ issues are: error handling, buffer management errors, numeric errors, directory traversal, and cryptographic issues. Java includes CRLF injection, code quality, information leakage, cryptographic issues and directory traversal.
The top issue plaguing both JavaScript and PHP is cross-site scripting, while Python’s top flaw is cryptographic issues.
“It’s unrealistic to expect that developers will write project code every time they work on an application, but it’s critical that they’re enabled to find and fix flaws on a schedule that won’t create more of a bottleneck. Implementing secure coding practices and increasing developer known-how for flaws by language can help ensure that the security of your applications (and your sensitive data) is where it needs to be to keep up with modern software development,” the company stated in its State of Software Security: Flaw Frequency by Language report.
The full list of issues is available here.






