Websites are playing a critical role for the candidates in the 2016 U.S. presidential primary season. These sites are used to encourage voters and educate the people of their platform, but even these candidates are susceptible to hacks and security problems, impacting their campaign or their image.
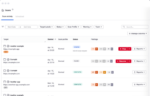
Each presidential candidate has a website, but which tops the charts in terms of the most secure site? Alex Heid, chief research officer at SecurityScorecard, a service that rates the security of an organization, decided to do some research.
He found that many candidates are making use of CloudFlare, a common distributed denial-of-service (DDoS) mitigation platform that works as a Web application firewall. There might be other protections in place, but CloudFlare is readily observable through the routed IP addresses, said Heid.
(Related: Security dominates this week’s Strata Conference)
In his research, he found that republican candidate Donald Trump’s website ranks at the top in terms of security, with democratic frontrunner Hillary Clinton lagging behind. Heid’s analysis also looked at the Ted Cruz’s, John Kasich’s and Bernie Sanders’ campaign websites.
His SecurityScorecard analysis of the presidential candidates’ websites did not involve any invasive penetration testing. Instead, it was based on passive analysis. He was able to get information by looking at the IP addresses and by viewing the source code of the given website.
“By using Google, we were able to determine which sites were the official political campaign websites,” said Heid. “The technique of ‘Google Dorking’ was also used to attempt to identify technologies the website used. Google Dorking is slang for advanced search queries that drill down on search results to very specific items.”
Heid also found that sites that belong to the Cruz, Sanders and Trump campaigns all use DDoS and Web application firewall (WAF) protection from CloudFlare. The Clinton and Kasich websites both are hosted on Amazon Web Services, and neither had DDoS/WAF protection in place, according to Heid’s analysis.
While Trump’s site seems secure, he has recently been called out by the hacker group Anonymous, which targeted Trump by “doxxing” him (which means to release personal data), said Heid.
“There have been previous successful breaches by hackers at Trump businesses throughout the years,” he said. “However, it seems the Trump campaign website has not yet been publicly breached.”
Heid also said that the site seems to be under a constant DDoS attack, as evidenced by CAPTCHAs that occasionally appear on the homepage. These CAPTCHAs can appear for many reasons, but they mainly do so against floods of traffic.
“I noticed the appearance of the CAPTCHA the day that Anonymous released the doxx and declared battle,” said Heid. “So the site has not succumbed to any attacks yet.”
Besides determining who had the most secure website, this research allowed SecurityScorecard to see how seriously candidates took their own digital security, he said. He added that the next president will be faced with issues of cybersecurity for the entire nation, and the organization figured that this research would be a good indicator of how they will treat the responsibility as president.
And as the election comes closer to the end, new vulnerabilities will be released, updates may or may not have been patched, and several other factors leading to a cybersecurity incident could occur, said Heid.
“It will be interesting to see what kind of impact it will have to the overall campaign,” he said. “Information security issues have never played so important a role in a political campaign as during this cycle.”