Ironclad Encryption Corporation today announced the availability of ICEMicro, the world’s first context-free and natively-secure container that enables all developers to take ownership of application data security. Utilizing ICEMicro, any developer can secure communication between containers across disparate scheduling and orchestration platforms, IaaS services, transport-layer security protocols, and on-premises or hybrid environments using Docker-compatible hypervisors. ICEMicro gives DevOps teams a way to build, deploy and run secure applications without the costs associated with legacy security strategies.
ICEMicro “Community Edition” images are available free now via Github and Docker Hub .
“ICEMicro is the simplest, most effective, and reliable means of securing vulnerable communications between docker containers,” said JD McGraw, president and CEO of Ironclad Encryption. “Up to this point, unmanageable encryption overhead has prompted developers to transfer encryption responsibilities to business operations, ultimately inflating costs.”
To date, inter-container communications have not been addressed adequately by existing container orchestration frameworks and protocols. ICE Micro changes that by providing developers with a natively secure container image to package application code. Since secure communications are an inherent feature, any two ICEMicro containers can communicate securely “out of the box.”
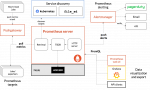
ICEMicro includes: “ICECube,” a native Docker container TLS solution that ensures low-overhead communication between containers; “ICEMan,” a symmetric TLS library written in Python that encrypts and decrypts egress and ingress layer 4 traffic (respectfully) using configurable symmetric encryption TLS cipher suites; and “ICECore,” Ironclad’s proprietary and patented technology that abstracts Docker services into a Trustplane. The Trustplane secures data in transit simply and reliably, allowing developers to ensure data integrity without concern for Data Plane and Control Plane configurations or security vulnerabilities. With applications running in natively-secured ICEMicro containers, VPNs are no longer the vulnerable and expensive chokepoint that limits multi-environment deployments.
Developers will gain significant speed and efficiency using ICEMicro, as securing communications between two containers is accomplished as quickly as applications can be created. ICEMicro does not require additional development overhead or network security expertise.
“The ICECore library is 2.5 times faster than the most used open source python crypto wrapper, meaning that cross-platform networks can now be effectively secured without suffering unacceptable latencies,” said McGraw.
Secure Communications Between Docker Containers
ICEMicro allows developers to secure communications between two containers in as little as 5 minutes which is ideal for DevOps teams utilizing Continuous Delivery practices. Using ICEMicro, developers can ensure security between containers that are running on:
- A single IaaS platform and a single Docker management platform such as Amazon Web Services (AWS) and a local Kubernetes deployment.
- Multiple IaaS platforms such as Google Compute Engine (Kubernetes) and AWS EC2 Container Service (ECS)
- Hybrid IT environments such as colocation (hypervisor) and AWS ECS
Unlike most current strategies, ICEMicro does not depend on the transport layer for data security. However, it is compatible with any transport layer security protocol. Transport layer security protocol vulnerabilities are well known. As quickly as protocol upgrades are deployed, hackers exploit new vulnerabilities. Networks deploying legacy TLS pose even higher risks. ICEMicro is agnostic to the TLS protocol and natively secures the communications between containers within legacy or greenfield environments, limiting successful TLS hacks access to encrypted data only. Essentially, ICEMicro renders TLS unnecessary.
“ICEMicro is ideal for software and embedded software developers who want to secure communications between applications, between devices including IoT devices or between applications and devices,” said McGraw. “The use cases are limitless in any industry, let alone across industries.”