It wasn’t long ago that some very smart people on the Internet saw that countries like China, Burma, and eventually even the United Kingdom were trying to control what their citizens did on the Internet. To combat this authoritarianism online, the Tor project was created.
Tor is, essentially, a network of proxies around the world that take away your identity. When you sign onto Tor, you’re going through an access node located somewhere in the world, likely run by people who are spending their personal funds on hosting something that they feel is helping people who are living in tyrannical states. Tor also allows servers to be hosted anonymously, giving dissidents a place to store files and communicate.
Today, Tor is a thriving project, and as stated before, it’s even of use to Brits who were stuck when the country started filtering porn off its Internet feeds (and in doing so, blocked legitimate sites). Tor has nodes hidden away in places like MIT, Noisebridge, and German universities. And even though Tor is used by people to do illicit things, such as share illegal pornography or even sell drugs via the now-defunct Silk Road, no one in the U.S. has ever been prosecuted for hosting a Tor node.
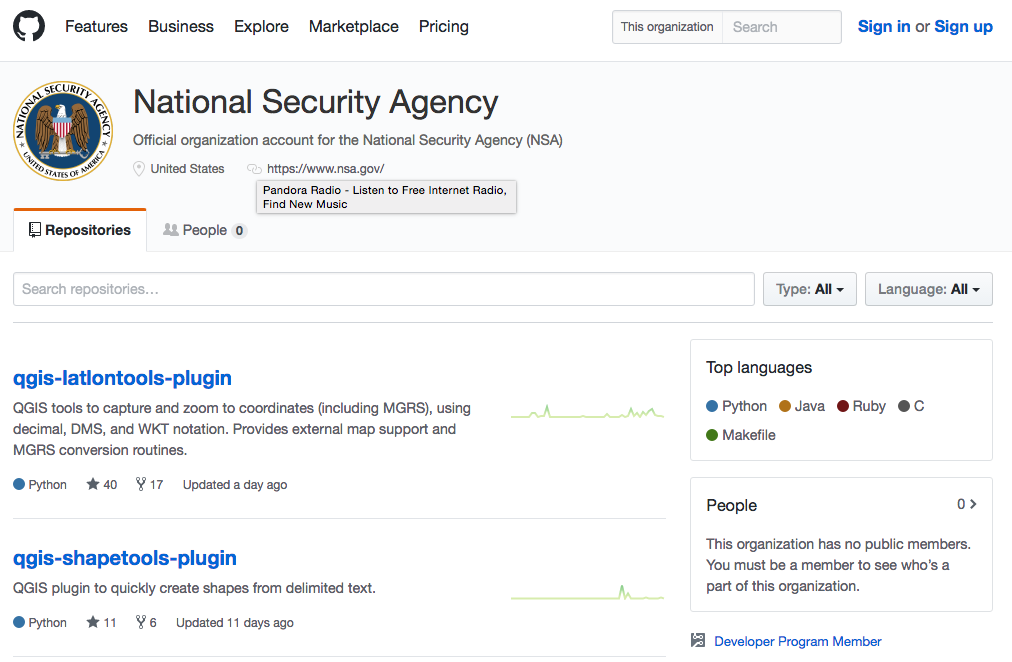
(Related: Another safe project from the NSA)
They have, however, received visits from the FBI.
Tor is the backbone of the anonymous Internet, and clearly the NSA hates it with a passion. Or, at least, it did until it began to realize that Tor nodes were great places to meet terrible people’s IP addresses. Now, Tor itself has never been compromised: It remains secure and anonymous. But to get to Tor, you have to use a Tor node, and to get to a Tor node, you must send info from your IP address to the node’s address. And even before that, you’ve got to download the list of Tor exit and entry nodes from the central authority.
And this is where the NSA has decided it can have the most fun: by monitoring and even running its own Tor nodes. A German news outlet working with some friends of mine has released a scathing report on just how the NSA monitors Tor traffic. Specifically, the NSA is tagging IP addresses that come to Tor nodes and watches them.
They’re especially watching anyone who knows about XKeyscore, a tool built at the NSA to do deep packet analysis of monitored traffic. If you’re interested in XKeyscore, you get tagged and followed by the NSA. Don’t go Googling that term!
But what’s far more frightening is that the NSA has, effectively, built a huge stack of offensive intrusion tools that can be automatically triggered by something like searching for information about XKeyscore. The entire Guardian suite of software can be sent off to break into your computer, no warrant needed, no international borders heeded.
This is obscene. This is the beginning of the end for human Internet freedom. When there are not even any hands on the wheel that’s driving the TCP tank, there’s something very wrong. It makes the NSA appear no less immoral than the script kiddies who fire off Metasploit attacks across huge ranges of IPs, then go back and turn the exploitable locations into zombies.
So, there you have it. The NSA has finally crossed the line from out-of-control security agency into the realm of rogue AI. Hopefully, you can all sleep better at night knowing you’re protected from security enthusiasts who use Google.