There are potential zero day exploits in the open source protocols and common file formats across six specific industries, according to Synopsys’ State of Fuzzing 2017 report. This includes the automotive, finance, industrial control systems, Internet of Things (IoT), government, and medical fields.
The report stems from more than 4.8 billion fuzz tests conducted by Synopsys’ customers in 2016 using its Defensics Fuzz Testing tool.
Fuzzing is a technology used to find vulnerabilities in software by sending malformed input to a target and then observing the result. Further investigation may be required if a vulnerability is exposed, and this technology is valuable to consumers of software and developers.
“Fuzz testing is a powerful component of the Synopsys Software Integrity Platform to uncover zero-day vulnerabilities and help organizations protect their software,” said Andreas Kuehlmann, senior vice president and general manager for the Synopsys Software Integrity Group. “By analyzing such a large data set from our customers, the Synopsys fuzzing report provides visibility into unknown, hard-to-find vulnerabilities and highlights where security teams should look to improve the quality and security of their software.”
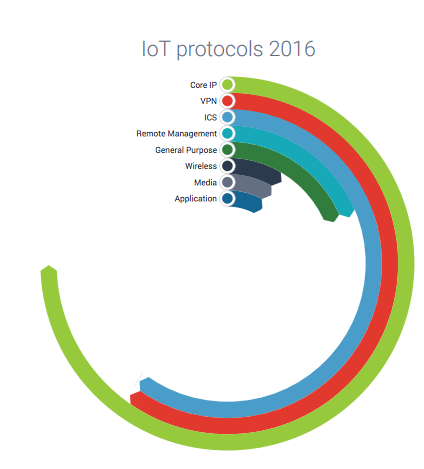
The report looks into the maturity of protocols used by different industry verticals. Certain protocols are more mature, or implemented better than other protocols. To measure the relative maturity of a protocol, the time to first failure (TTFF), or the time to the first instance of when a protocol crashes, is used.
Synopsys found that the overall average TTFF was 1.4 hours. In more mature protocols, the length of time is in hours, but with less mature protocols, this time could be as short as seconds. This indicates a higher likelihood of exploitable vulnerabilities, according to the report.
Protocols associated with ICS showed the most immaturity, according to Synopsys. The least mature protocol tested in 2016 was IEC-61850 MMS (ICS), which is a niche protocol used in IoT and industrial control systems. Its TTFF was 6.6 seconds.
Fuzzing found Core IP protocols that were well-implemented, like the TLS client, which was commonly used for secure web browsing including, online banking and e-commerce. The average TTFF for TLS was nine hours, according to the report.
Security pros have applied fuzz testing and application hardening tools on web apps for years, and these tools are becoming resourceful in the IoT market today, especially since applications are difficult to crawl with traditional testing tools, according to a recent Forrester Research report.
The Forrester report also states that as IoT applications become more prevalent, fuzz testing and application hardening tools will soon have “a rebirth.”






